Trends

Search Trends
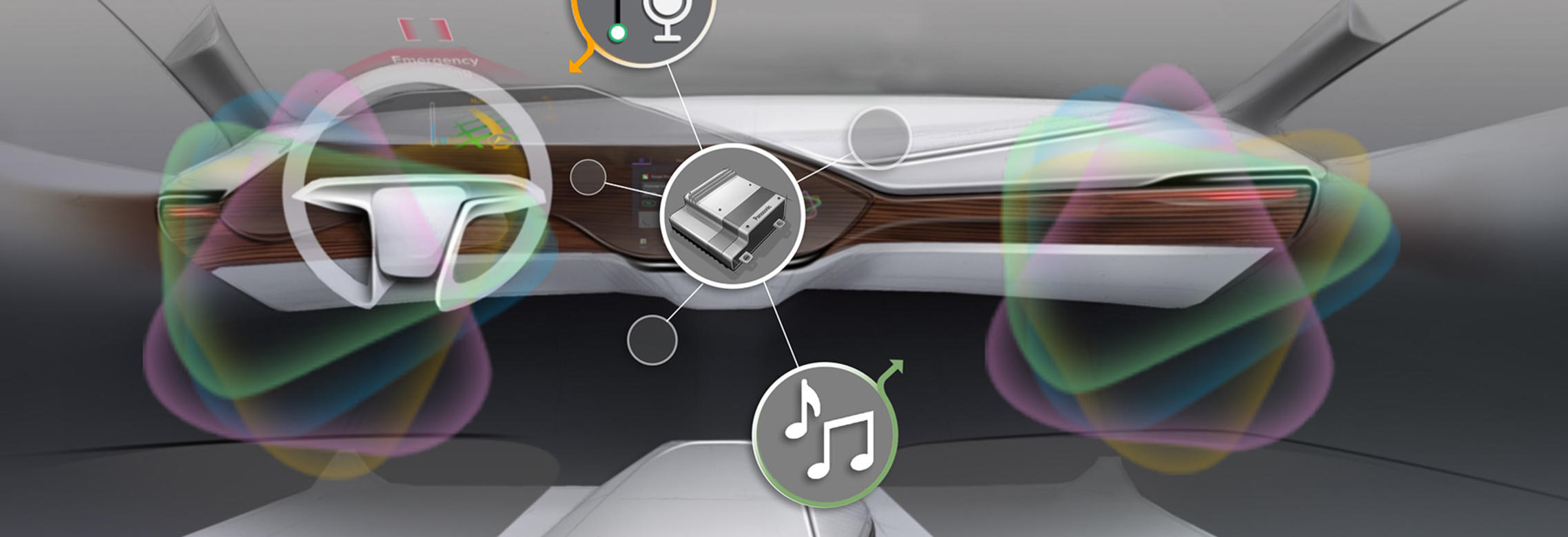
Welcome to ideas for a connected world where cities spontaneously adapt to the needs of people, cars talk to each other to avoid accidents, and planes keep passengers in touch with their lives on the ground below.


At iconic stadiums and concert venues, museums and theme parks, and events like the Olympics, our technologies immerse fans in the action and inspire and amaze. These are experiences you just can’t duplicate at home.

Eureka! Here’s a look at Panasonic’s brightest new ideas, inventions and brainstorms that are helping businesses and economies to grow and governments to serve constituents in more efficient and novel ways.
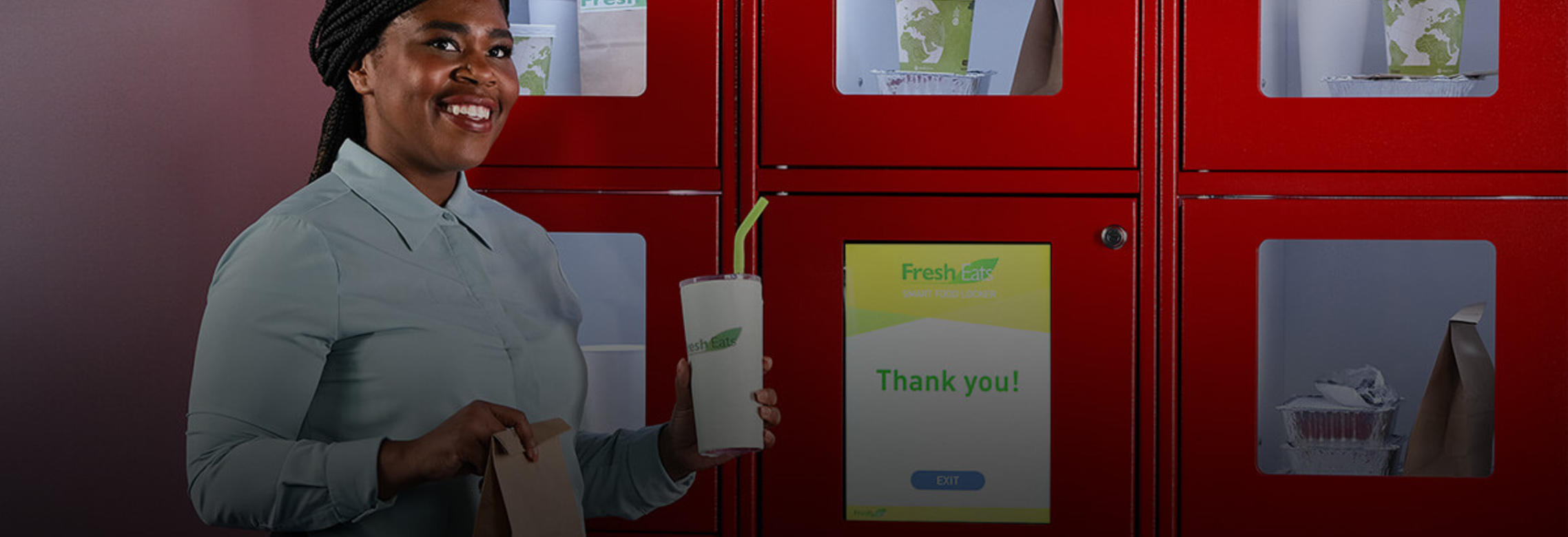
From factory floor to retail store, everything operates more seamlessly with Panasonic technologies. Processes manage themselves. Insight and intelligence informs operations. It’s all about achieving peak efficiency.

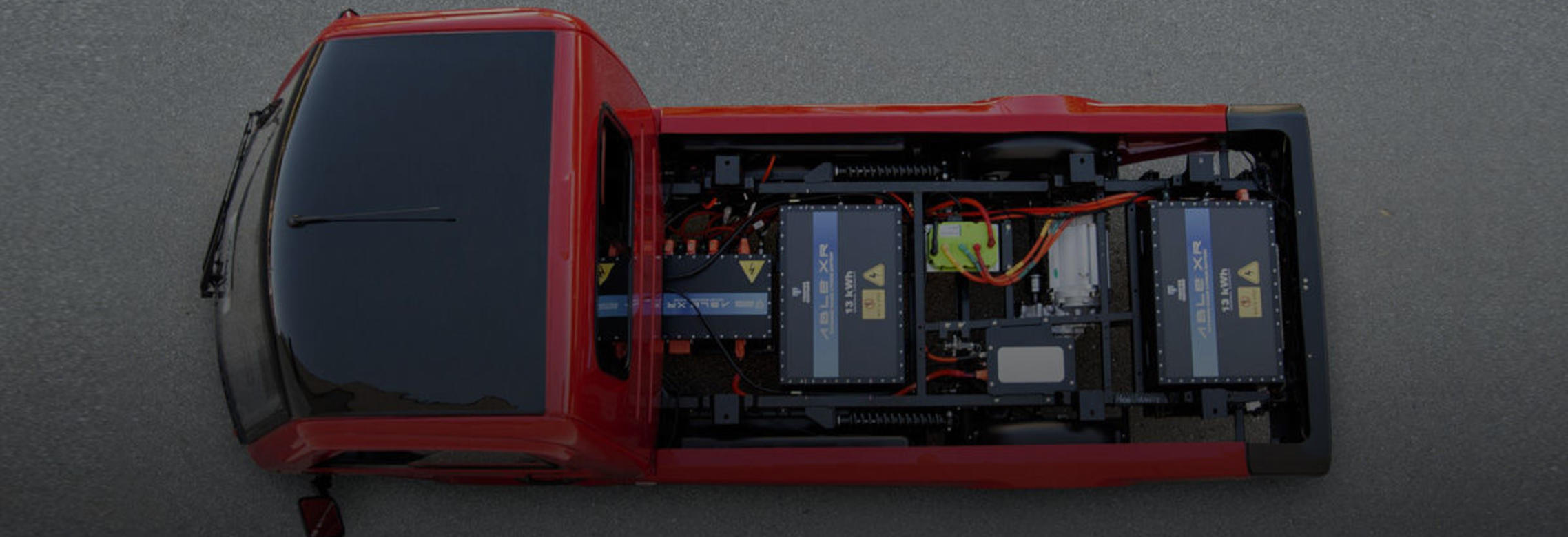
To uncover fresh ideas on technologies including advanced robotics, autonomous vehicles and the IoT, we conduct studies and proprietary research to help business and government leaders make better decisions. Here is a look at some of our newest findings.
"Contribution to society” has been among Panasonic's core values since our company was founded over a century ago. Our mission is to improve lives and create a better world for all – and we’re turning our beliefs into action.
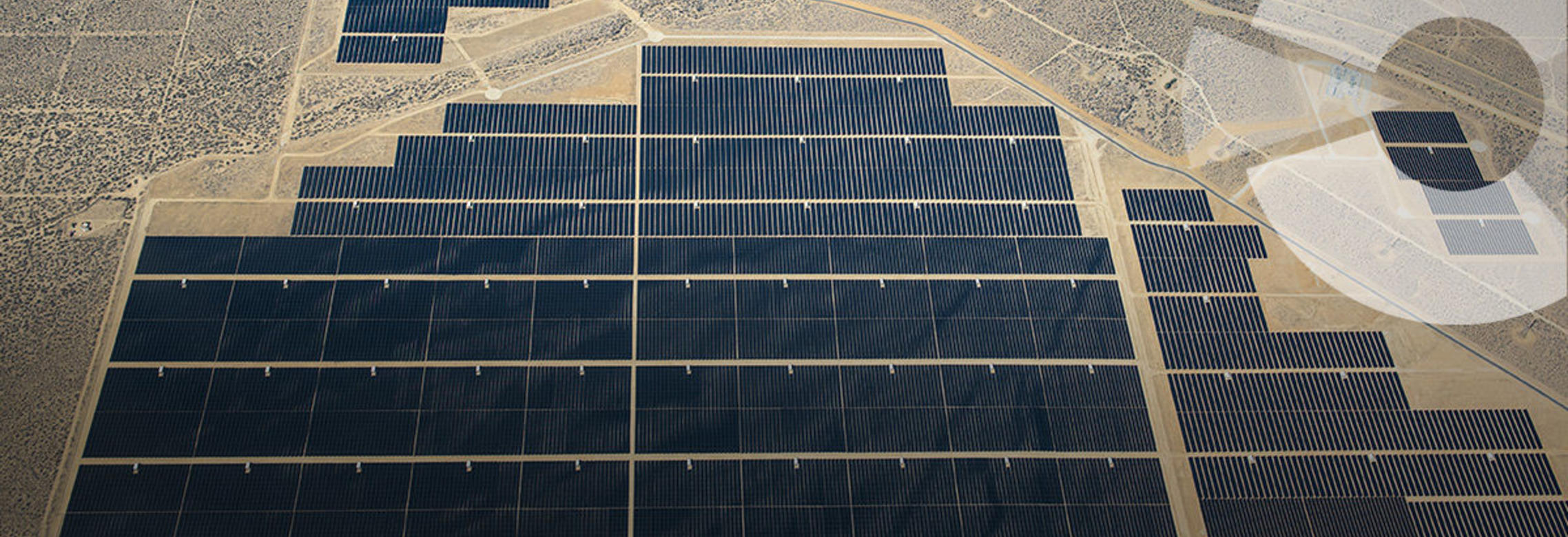
We’ve long focused on creating a more sustainable planet–from taking charge of electronics recycling to optimizing battery tech. As a result, we’ve become a world leader in breakthrough alternative energy technologies.